The Price of ‘Too Good to Be True’
Published: April 17, 2026 | Last Updated: April 17, 2026
The Price of ‘Too Good to Be True’
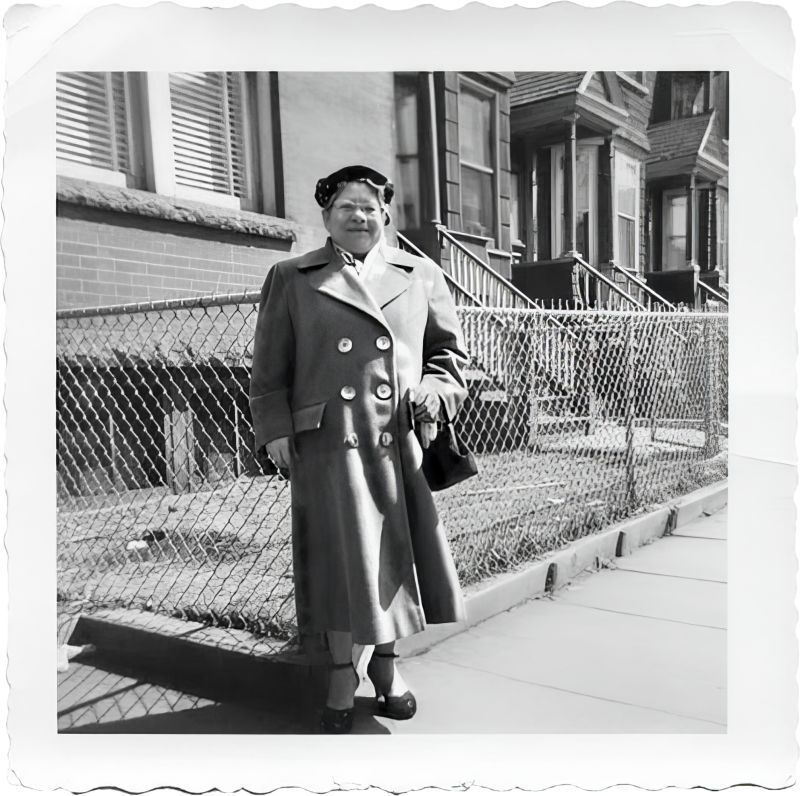
Grandma Tardanico loved a bargain.
Growing up in a matriarchal Italian household in the 1970s, we pinched our pennies and spent wisely. Poor Uncle Joey would bring Grandma meats, cheeses, and some pretty questionable wine from the city every week. Those in my generation might remember the green glass gallon jug with the little finger loop and a tin cap—that wine.
Grandma thought she was saving a fortune on her purchases, but in reality, there were agents in the background doing the footwork to make that “deal” happen.
I think about that often in today’s security landscape. Because just like Grandma, it’s easy to believe you’re making the smart investment without fully understanding the background costs—the ones that never show up on the first invoice.
The AI Security Gold Rush
The security market right now is flooded with vendors advertising AI-driven miracle cures. Everyone is showcasing Agentic AI as the answer to defending against modern threat actors.
Every CISO I know is dealing with the same thing—constant LinkedIn messages, trade show pitches, and requests for “just 15 minutes.” Every one of them promises protection against AI-powered attacks.
And on paper, most of them look incredible.
That’s part of the challenge. When everything looks great, it becomes much harder to separate signal from noise.
A New Kind of Adversary
At the same time, attackers are evolving just as quickly.
We’re now seeing threats that simply didn’t exist even a short time ago, including what I’d describe as AI swarm attack vectors. These are not isolated attacks. They are coordinated, adaptive, and continuously learning.
Where attackers once needed significant time to plan and execute, today’s threat actors are using Agentic AI to:
- perform reconnaissance across entire environments
- feed telemetry back into host systems
- rapidly test and refine new attack paths
What used to take weeks can now happen in minutes. These systems don’t just execute—they iterate, adapt, and evade in real time.
Our defenses have to operate at a level of sophistication that, until recently, wasn’t necessary.
The Vendor Dilemma
This brings us back to the vendor landscape.
Every solution sounds promising. I’d genuinely like to bring many of them in and see what they can do. But the reality is that evaluation itself is expensive. It pulls teams away from active defense, requires lab work and testing, and often introduces disruption without guaranteed value.
So the real question becomes: is it worth the cost just to find out?
In many cases, “trying before buying” is riskier than it sounds.
At the same time, vendors face their own challenge—how to differentiate in a market where everyone is making similar claims and using similar language. Earning a real seat at the table takes more than a compelling pitch.
Building While Defending
While navigating all of this, we’re also actively building.
We’re ramping up our own protection landscape with Agentic AI and machine learning tools, driven by teams who understand our environment and operational needs. These aren’t perfect solutions, but they’re built by people we trust—people who can debate, deploy, and move on quickly when something doesn’t work.
That ability to iterate quickly is becoming just as important as the technology itself.
No Playbook Yet
There is no universal runbook for this new reality.
Some vendors will claim they’ve built one, but adopting any solution still requires time, focus, and resources that security teams don’t always have. While attackers are testing and refining AI-driven attacks 24/7, security teams are still managing reporting, compliance, internal coordination, and everything else that comes with the job.
It’s not simply a question of adding more people. Even at larger scale, teams are still operating against adversaries that don’t pause, don’t slow down, and don’t run out of cycles.
The Expanding Challenge
Adding to the complexity, AI adoption isn’t limited to security.
Every part of the business is exploring how to use AI—finance, marketing, sales, operations—and that creates new governance challenges, new risks, and new dependencies. Security teams are expected to support and secure these initiatives while continuing to defend against increasingly advanced threats.
There’s also a growing infrastructure burden. Telemetry, logging, monitoring, and auditing all need to evolve to keep up, ensuring that the organization’s own AI capabilities aren’t turned against it.
Example
One pattern we’re beginning to see is coordinated probing across environments, where multiple AI-driven processes test different entry points simultaneously. These systems feed results back into a loop, refining each new attempt based on previous outcomes.
Individually, these actions can look like low-level noise. Together, they represent a coordinated, persistent effort that adapts continuously and becomes more effective over time.
Where This Leaves Us
Security budgets continue to grow, but so does complexity. More tools don’t necessarily lead to better outcomes if they introduce overlap, gaps, or operational friction.
Most organizations are still working to close the gap between detection and response while managing an increasingly fragmented environment. Tool sprawl, competing priorities, and limited time all contribute to that challenge.
There isn’t a simple answer yet—only a series of tradeoffs that every CISO has to navigate.
Let’s Compare Notes
I’d be interested to hear what you’re seeing.
We’re actively building, testing, and adapting, and there’s real value in comparing perspectives across teams facing the same challenges. If this reflects what you’re seeing in your own environment, reach out to me on LinkedIn to continue the conversation or better yet, come up to the house and I’ll see if I can dig up some of Grandmas questionable wine.
Paul Mazzucco, SVP and Chief Information Security Officer
